ABOUT
KH IT SERVICES LLC
At KH IT Services LLC, we are at the forefront of digital innovation, providing cutting-edge IT solutions and services that empower your business to thrive in a rapidly evolving landscape. Our mission is to ensure your organization operates at peak efficiency, leveraging technology to drive growth, enhance security, and optimize operations. As a forward-thinking partner, we specialize in a comprehensive suite of services tailored to meet the demands of modern businesses, including: Managed Services Provider (MSP) Solutions, Telecom Sales & Infrastructure Services, Microsoft Government and Community Cloud Solutions, Advanced Networking Solutions, and much, much, more.
KH IT Services proudly holds certifications as a State Certified HUB (Historically Underutilized Business) and City/Federal Certified MBE/DBE (Minority Owned Business Enterprise/Disadvantaged Business Enterprise). Our commitment to excellence and diversity drives us to deliver superior solutions that align with our clients’ unique needs.
MONITORING & ALERTING
Our security centric remote monitoring and management platform.
AN ARSENAL OF MONITORING TO ENSURE THAT YOU GET A CRISP VIEW OF YOUR INFRASTRUCTURE.


ENDPOINTS
Software monitoring, the low-footprint agent runs across Windows and Mac endpoints using native platform data acquisition techniques. We monitor a host of information, including:
• Processors
• Running processes
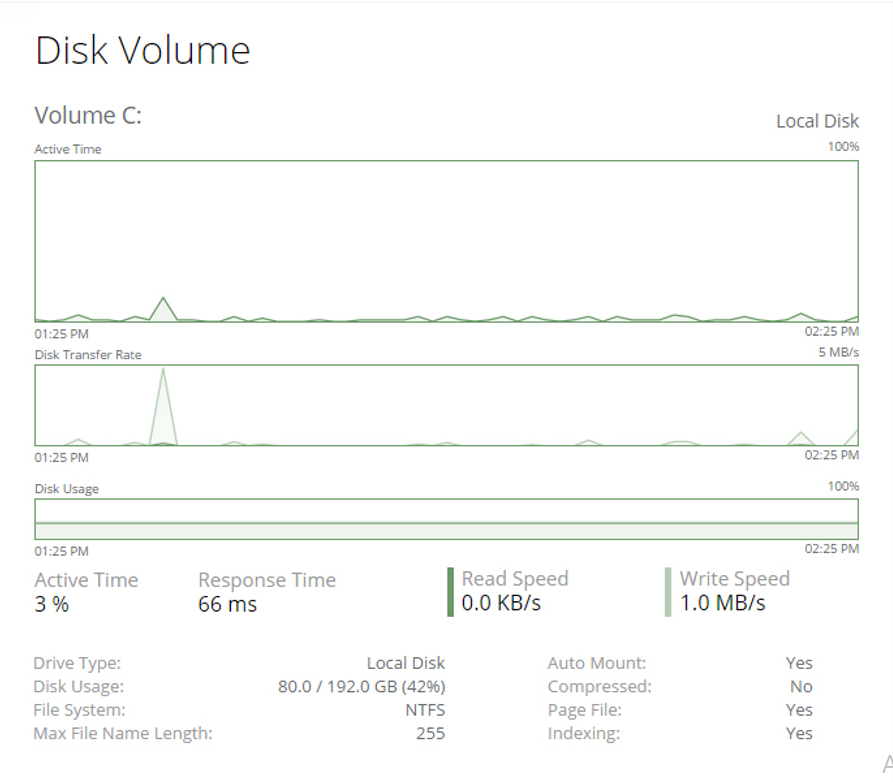
• Disk and volume information and usage
• Memory
• Network adapters and utilization
• Public and private IP address
• Software and hardware inventory
• Services
• User logs
• Event logs
• Microsoft Security Center status
• Windows product key
• Device serial number
• Many more!
CLOUD
Our cloud engine can externally monitor all aspects of your Internet-facing infrastructure. It’s perfect for application servers and websites, with features including
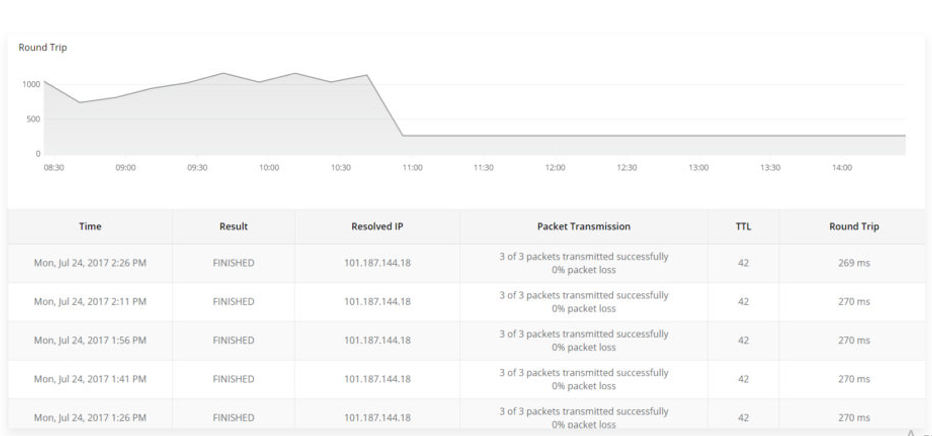
• Ping latency and availability
• Port compliance on inbound ports
• DNS resolution with response times
• HTTP GET and POST requests for website and external system monitoring
• Email monitoring of sent and received emails to verify the health of email servers* Extra
TRACK CHANGES THROUGHOUT YOUR INFRASTRUCTURE AUTOMATICALLY
NETWORK
We deploy our network management agent to monitor all printers, firewalls, routers and switches. Leveraging SNMP, NetFlow, Syslog, Traps and configuration backup, we support remotely monitoring thousands of network devices across many vendors.

ACTIVITIES
• Capture, trace and audit changes to your infrastructure
• Get a real-time feed of system activities
• Track how technicians are using the system and log all changes
• Create notifications for all device and system level events
• Log a suite of varying activities without having to create a configuration
• Setup required, activities will start populating as soon as the agent is deployed
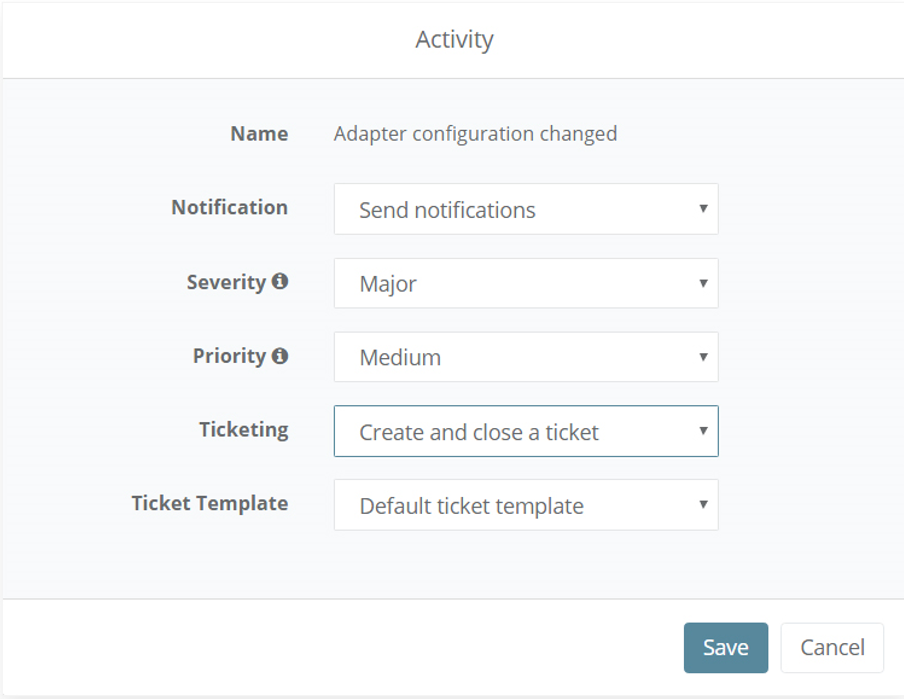
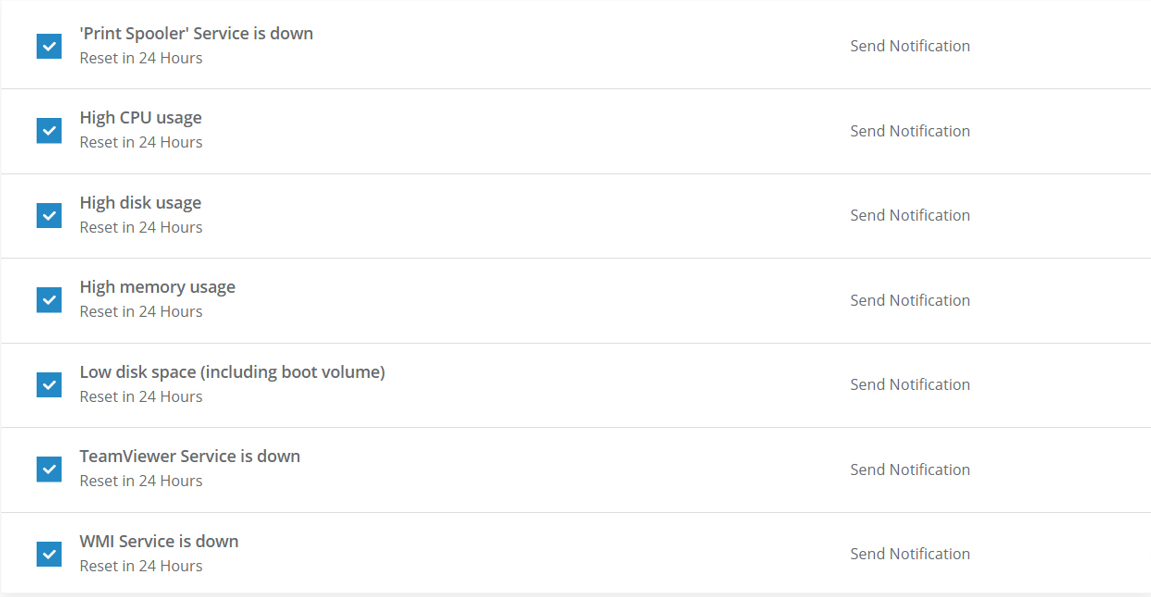
NOTIFICATIONS
We receive triggered alerts by SMS and email.
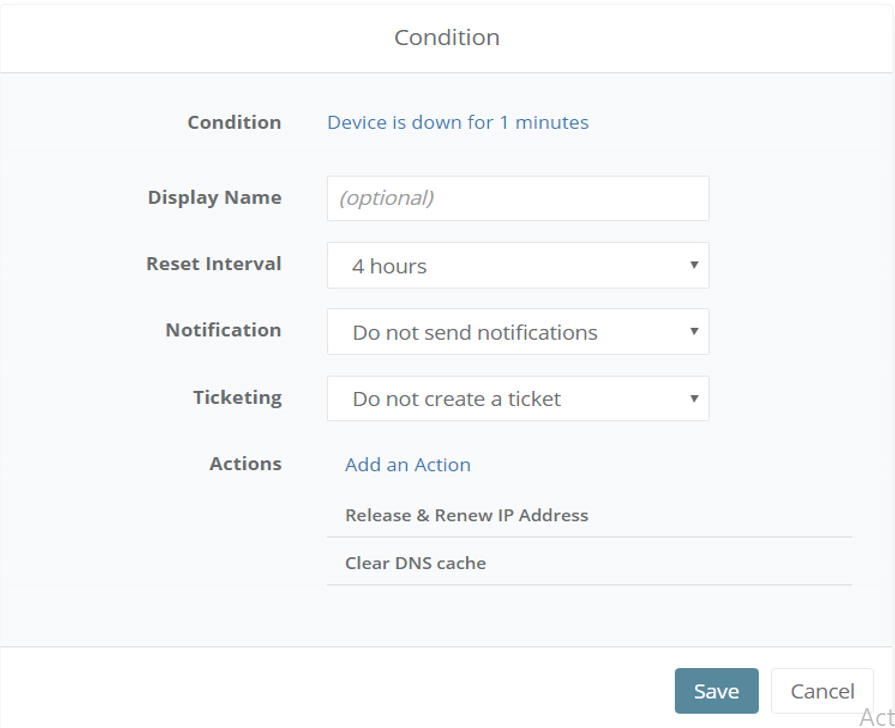
REMEDIATION
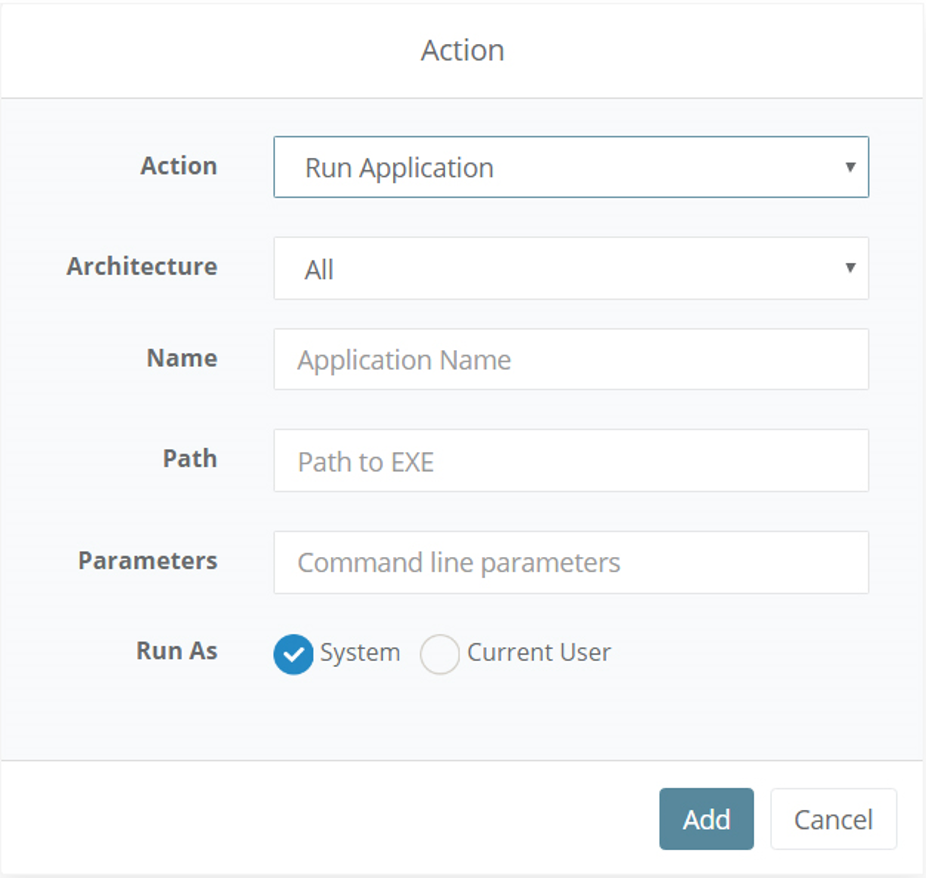
Upon any triggered condition, we can set up a series of automated actions to solve potential problems including:
• Running an application
• Running a command line
• Running a custom script
• Start, restart, and stop Windows service
• Start, restart, and stop Windows processes
• Reboot the endpoint
• and many more
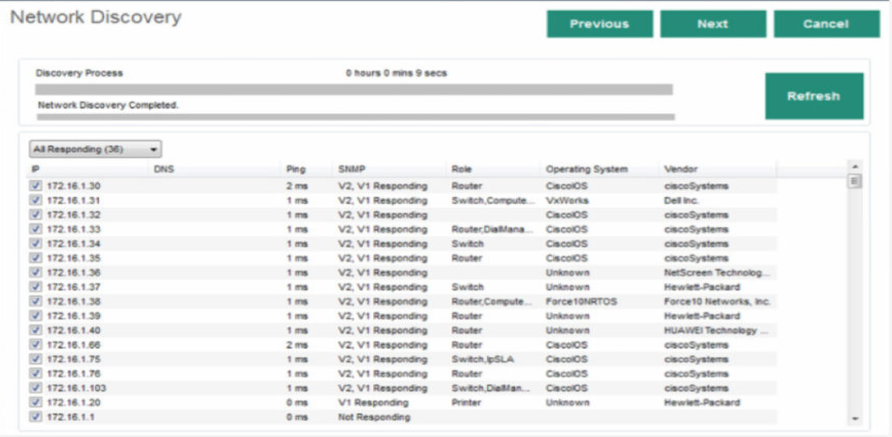
NETWORK MANAGEMENT
We deploy our network management agent to monitor all printers, firewalls, routers and switches. Leveraging SNMP, NetFlow, Syslog, Traps and configuration backup, we support remotely monitoring thousands of network devices across many vendors.

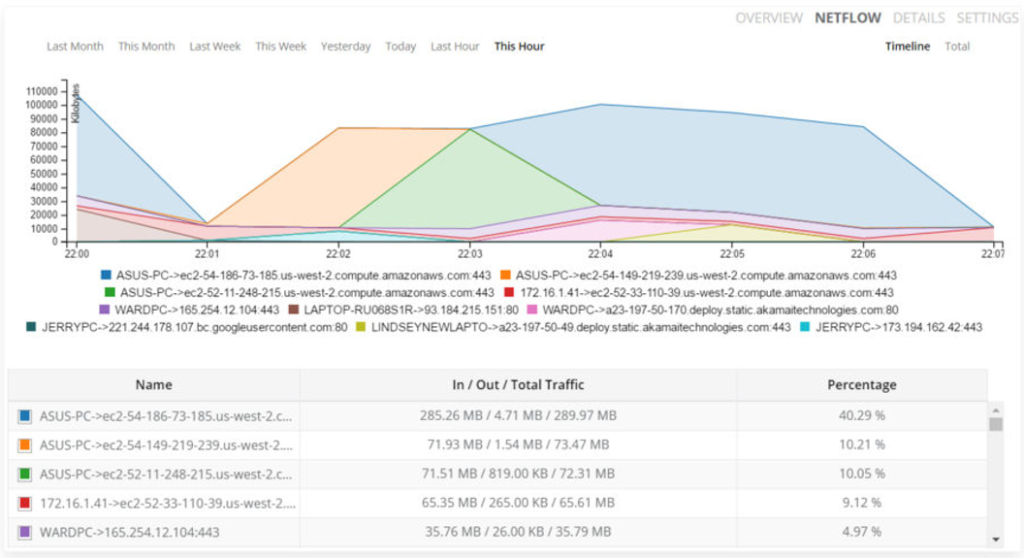
NETFLOW
• Detect network bottlenecks through integrated NetFlow monitoring
• Identify top network conversations, applications, domains, users, and endpoints for troubleshooting
• View NetFlow data by the hour or view aggregate data across longer periods of time
• Identify top users, domains, conversations and endpoints for troubleshooting
• Supports NetFlow v5, v9, and IPFIX
NETWORK DISCOVERY WIZARD
• We discover new network devices via our integrated wizard
• We hand-pick the credentials required to identify devices and perform tests ranging from a basic ping scan to an actual SNMP scan to determine device types and roles
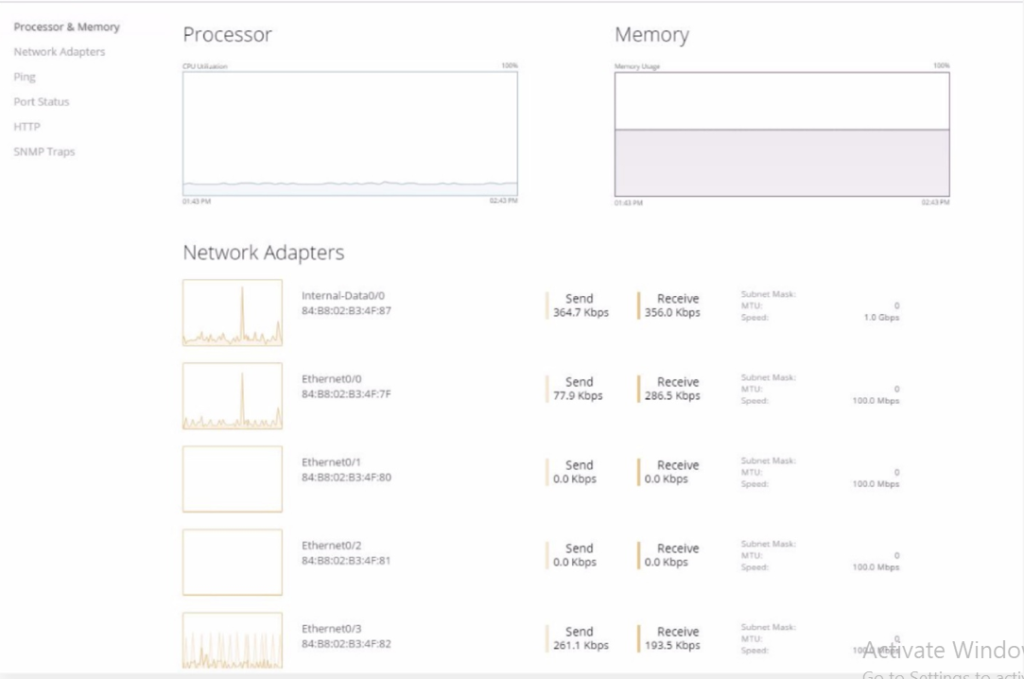
SNMP MONITORING
• We monitor common SNMP parameters, including processors, memory, network adapters, port status and SNMP traps
• See how your devices are performing and if any bottlenecks need to be addressed
SYSLOG COLLECTION
• We monitor Syslog data, including facilities and severities
• We research to holistically see the health of your networking equipment from a hardware and software perspective
• We selectively toggle different environment variables to be notified via Syslog messages

AUTOMATION
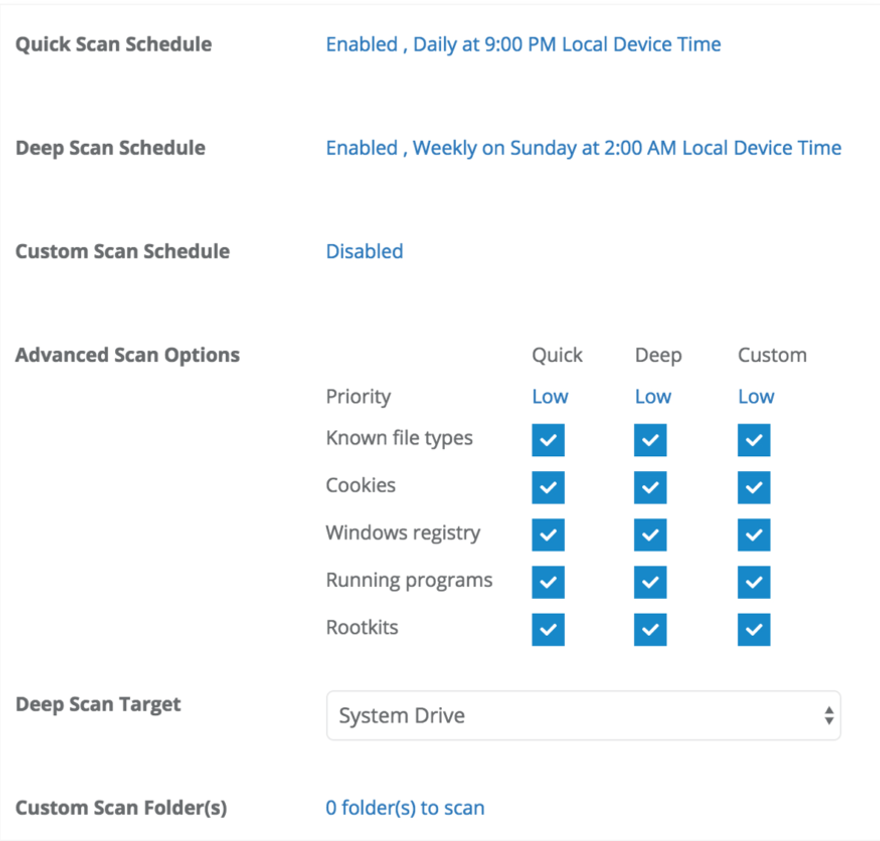
Our powerful policy framework allows us to automate common IT tasks and maintenance routines. We customize your alerting conditions, automate your maintenance tasks and manage patches and antivirus updates.
We can use automation to:
• Customize script parameters and run them with or without admin privileges
• Run scripts on a custom schedule
• Upload software installers and deploy with custom command line parameters
• Install patches
• Deploy, configure, and run antivirus software* WebRoot users
ON DEMAND
We run all scripts and remediation actions on demand with full auditing and compliance tracking, so that you can track IT changes over time.
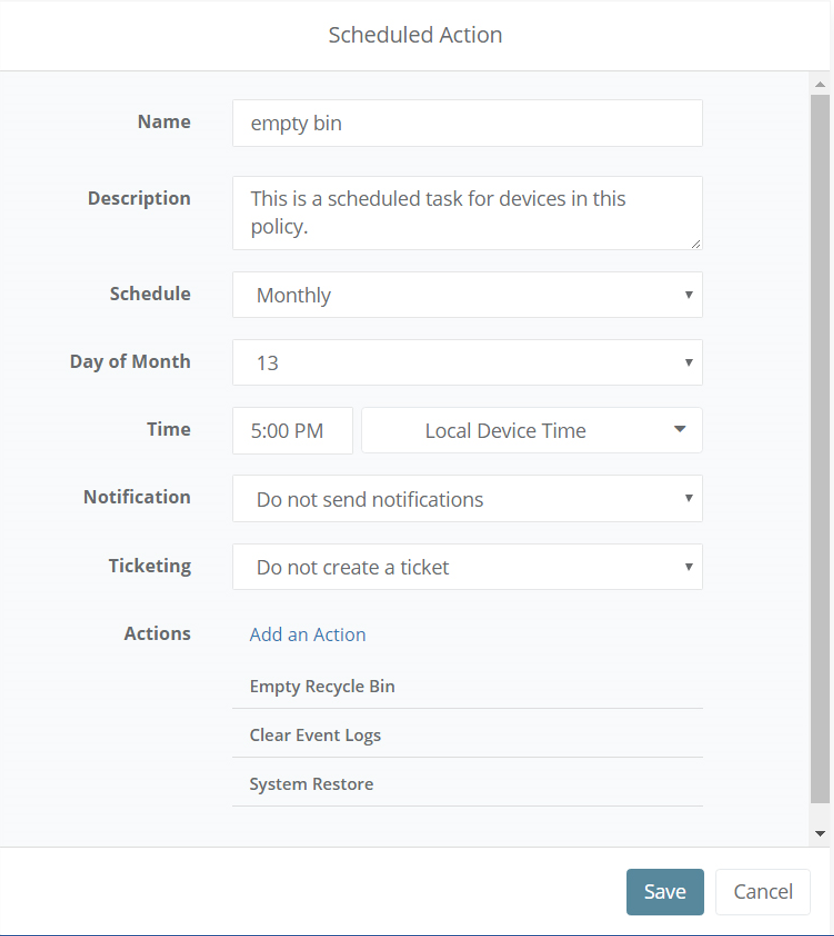
SCHEDULED
We schedule patch management, antivirus scans, scripts and more. We use scheduling for off-hours rollouts to your infrastructure, minimizing the impact on your organization.
AUTO REMEDIATE
Our software automatically repair IT problems by automatically configuring critical conditions based on a variety of performance thresholds and state change criteria.
POLICY DRIVEN
We use policies to drive automation configurations for mass deployment across devices and servers.
REMOTE ACCESS
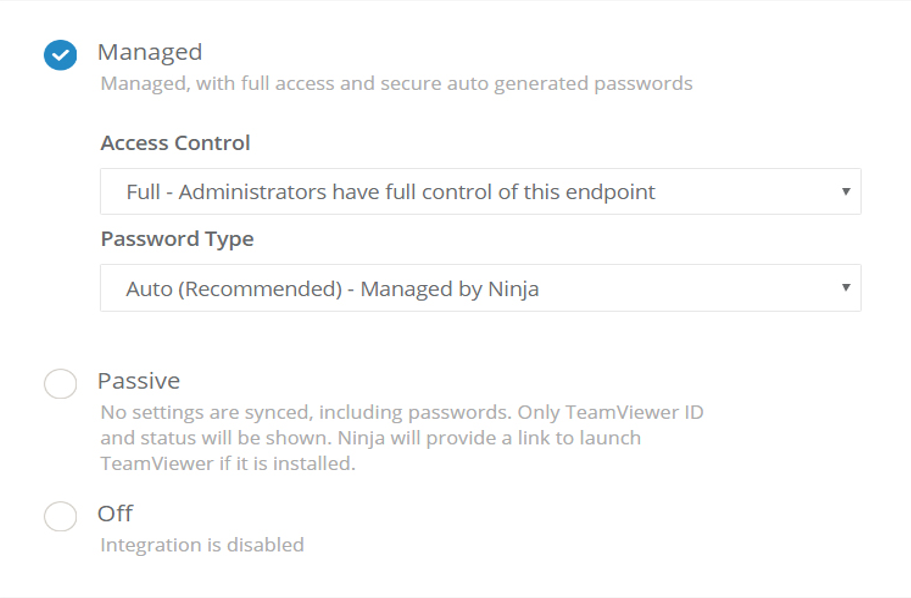
Securely and remotely access your devices from anywhere. We provide the best-in-class integrations of TeamViewer and Splashtop. Our software agent will deploy, configure, sync, and manage TeamViewer and Splashtop through a single-pane integration. You will be able to locate and connect to any Windows or Mac endpoints seamlessly.
We also provide a wide variety of built-in remote management capabilities. We can start/stop Windows services, kill processes, uninstall software, run custom scripts and remotely access command line without any user intervention.
TEAMVIEWER
We partnered with the best-in-class remote access tool TeamViewer. Your user license is automatically updated to the latest supported TeamViewer version (currently TeamViewer 14). In addition to remote access, TeamViewer provides powerful remote device management capabilities, including:
• File transfers
• Cross-platform support (connect from the desktop app, browser, or mobile app)
• Connections are secured through RSA 2048 public/private key exchange and AES 256-bit encryption
• User chat
• Remote audio/video
• Session recording
In addition to TeamViewer features, software agent and TeamViewer integration adds management and reporting features to provide a seamless IT remote support experience:
• We sync users, devices, groups, and user permissions continuously
• We can connect to synced devices through the TeamViewer mobile application
• We have detailed connection reports showing who connected to endpoints and exact duration.
• We use randomized passwords for enhanced security
• We support both attended and unattended access modes
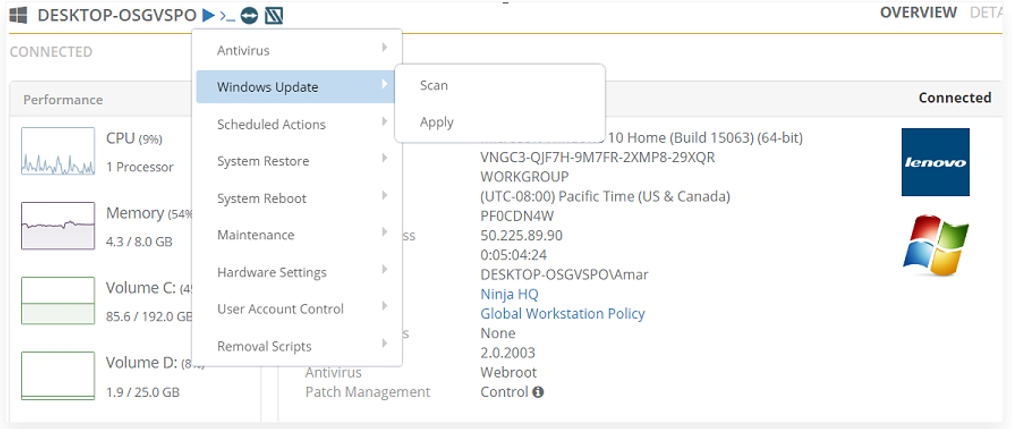
BACKGROUND MANAGEMENT
We provide a wide variety of built-in remote management tools so we can perform remediation actions without user interruption. Here are some of the powerful tools you can leverage:
• Stop running processes
• Start, stop, and restart Windows services
• Install and uninstall software
• Remote command line
• Execute custom scripts
• Force a disk error check
• Delete temporary files
• Enable or disable User Account Control
• Leverage over 50 other built-in actions
SECURITY (Symantec customers managed in Symantec.Cloud interface)
• We receive real-time alerts on threats
• We have integrated remediation options in our dashboard
• Initiate on-demand scans and schedule weekly scans
• Configure exclusions and quarantine files
• Multiple scanning options available directly from dashboard
• Report on active infections and past infections
• Report on antivirus protection and definition statuses to identify unsecured devices

Webroot is the next-gen endpoint security platform to protect your business against cyber threats. Webroot leverages security data across millions of endpoints to actively predict, detect, and prevent malware before expensive disasters occur. The agent is always connected to the cloud for the latest security bulletins and requires minimal system resources. Everything can be configured from the cloud: scanning schedules, file exclusions, path exceptions and even threat remediation. Easy rollbacks on compromised devices allow you to get them back up and running quickly.
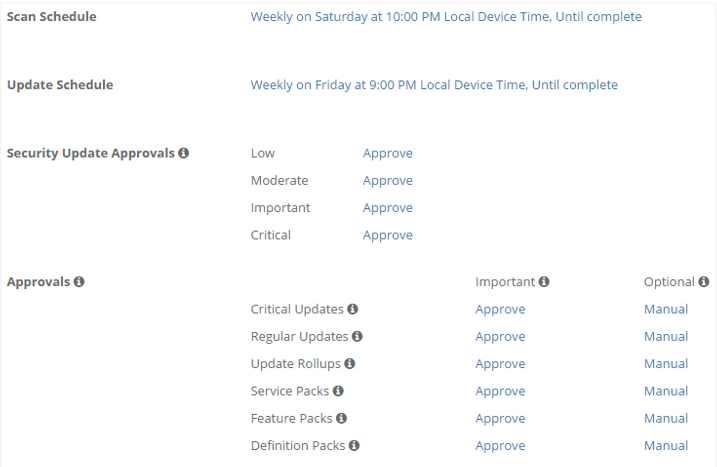
PATCHING
Leverage our Managed Services to manage Windows and third-party software patching. We customize your patching schedule to minimize user interference and you never miss an update through the built-in patching engine.
Patch Management Features:
• We utilize out-of-box settings to start patching endpoints with minimal setup
• We customize your scan and update schedules for different groups of devices
• We automate patch management through our powerful policy framework
• We manually approve or reject patches for specific groups or across all groups
• We have detailed patch compliance reporting to identify non-compliant endpoints
• We supports over 120+ common applications, such as Adobe, Chrome, Java, and more
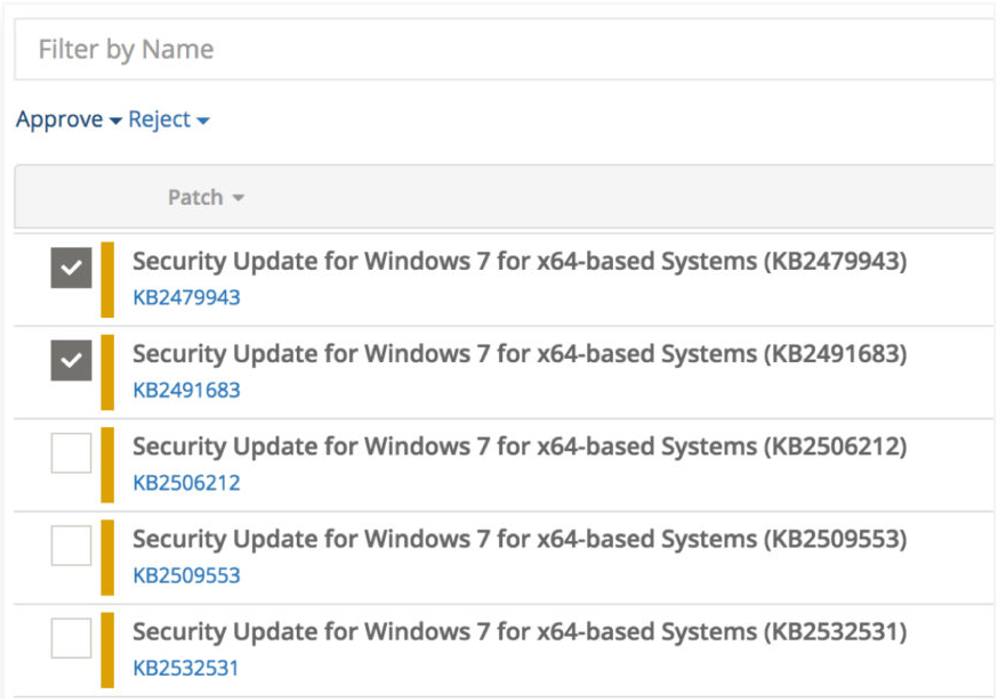
OS PATCHING
We automate Microsoft operating system patching across all major versions.
• Windows 10 (x86 / x64)
• Windows 8.1 (x86 / x64)
• Windows 8 (x86 / x64)
• Windows 7 (x86 / x64)
• Windows Vista (x86 / x64)
• Windows XP Professional, SP2+ (x86 / x64)
• Windows Server 2016
• Windows Server 2012 R2 (x64)
• Windows Server 2012 (x64)
• Windows Server 2008 R2 (x64)
• Windows Server 2008 (x86 / x64)
• Windows Server 2003 R2 (x86 / x64)
• Windows Server 2003, SP1+ (x86 / x64)
• Windows Embedded 8.1 (Industry Pro and Enterprise versions)
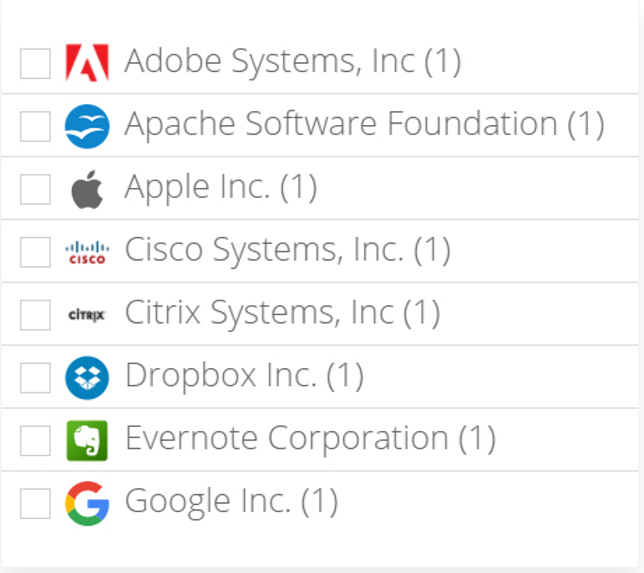
THIRD-PARTY PATCHING
Out integrated third-party patching engine will align your IT with the latest updates required by common office applications. With support for over 120+ software vendors, we will ensure your environment stays up-to-date and be protected from cybersecurity threats. Below is a sample of software vendors that we support:
• Adobe Systems, Inc.
• Apache Software Foundation
• Apple Inc.
• Autodesk, Inc.
• Box, Inc.
• Cisco Systems, Inc.
• Citrix Systems, Inc.
• Dropbox Inc.
• Evernote Corporation
• Google Inc.
• Hewlett-Packard Company
• Microsoft Corporation
• Mozilla
• Novell, Inc.
• Oracle Corporation
• Sophos
• Symantec Corporation
• TeamViewer
• VMware, Inc.
• Wireshark Foundation
ORGANIZATIONAL SNAPSHOT REPORTING, SCHEDULED, ON DEMAND AND ADVANCED SEARCH AT OUR FINGERTIPS.
MANAGED SERVICES FEATURES BULLET POINTS
24/7/365 Proactive device monitoring
• We make contact with Servers 24/7/365
• Performance health reporting
• Antivirus updates
• Network Firmware upgrades
• Microsoft® WindowsTM patch management
• Apple Device Monitoring and Maintenance
• Comprehensive software support
• Device inventory report
• Enhanced security
• Firewall support
• 24/7/365 Network monitoring
• Onsite technical support
• Hardware support
• 24/7/365 Server performance monitoring
• User identity and network access management
• Data Backup Monitoring
• Desktop Deployment
REPORTING
Leverage our robust reporting framework to run executive summaries, asset inventory, connection reports, and more. Below are examples of reports generated our platform that our clients love:
• Executive summary report to get a high-level overview of IT organization’s health
• Report on devices that generated the most alerts
• Asset summary of workstations, servers, and network devices
• Netflow traffic reports
• Connection reports of TeamViewer and/or Splashtop activity
• Patch compliance reports across different device groups and locations











